The True Cost of Ransomware Recovery: Ransom, Fees, and Downtime

SafePay Ransomware: Threat Profile and Analysis

16 Billion Password Leak: How to Protect Your Business
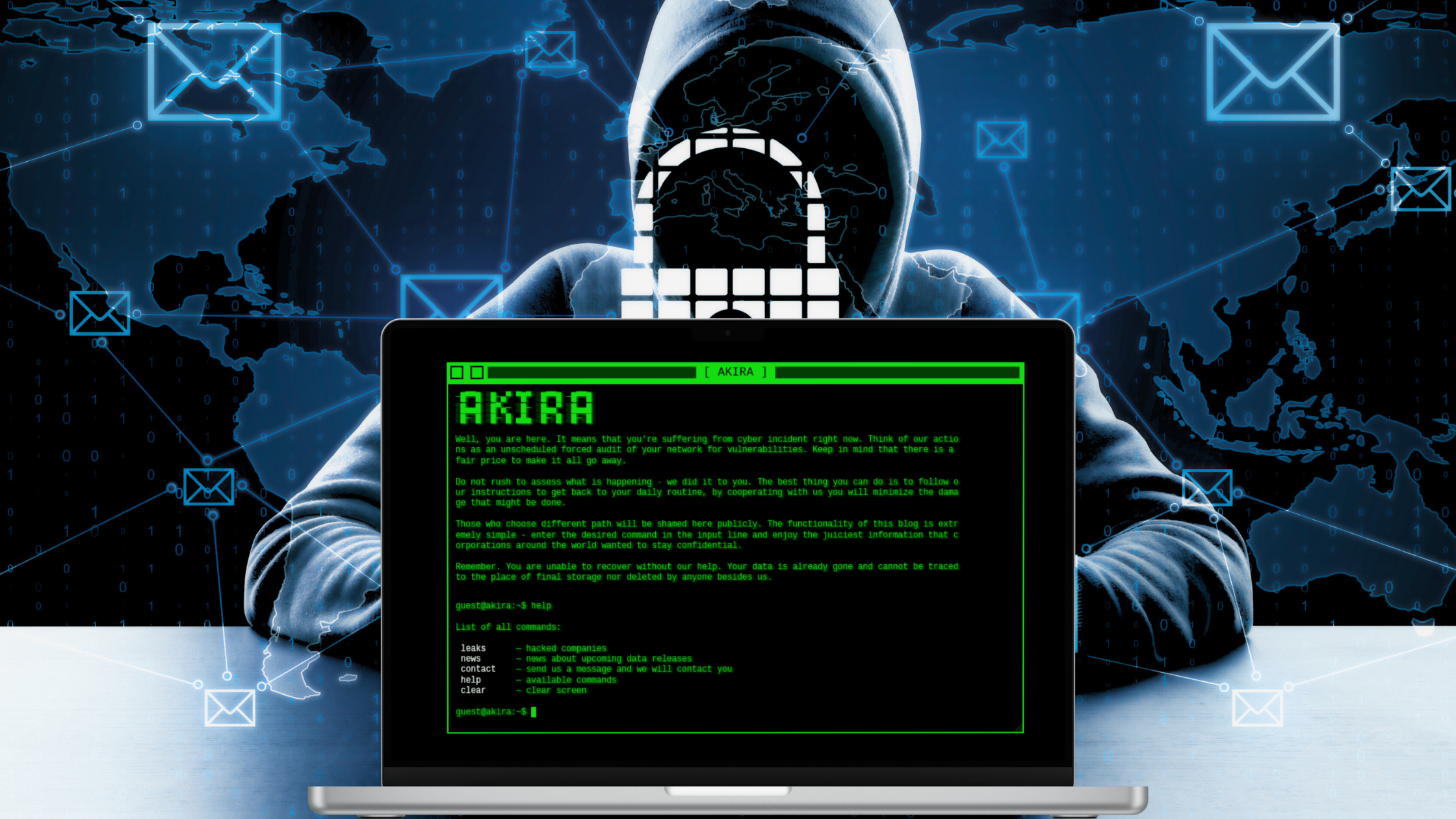
Akira Ransomware: In-Depth Technical Analysis

What is Cyber Incident Response & Immediate Steps

The Magento Supply Chain Attack: Full Story of What Happened and Why It Matters

How to Recover from a Cyber Attack: A Comprehensive Guide for Businesses

How Does Ransomware Spread: 12 Common Infection Methods